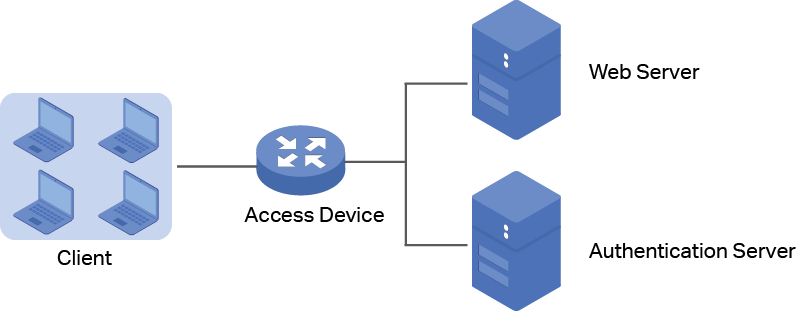
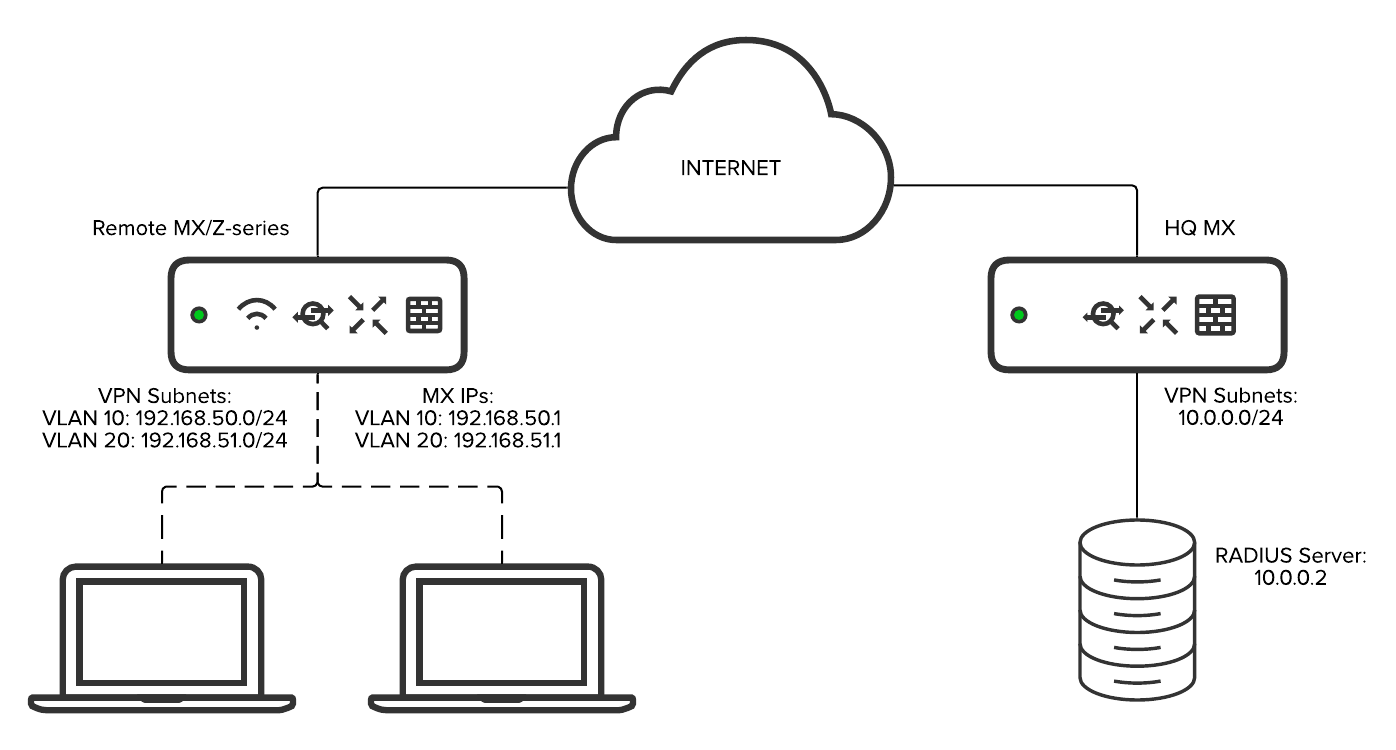
IEEE802.1X Authentication Settings - Canon - imageRUNNER 2545Wi / 2545W / 2535Wi / 2535W / 2530W / 2525Wi / 2525W / 2520Wi / 2520W - e-Manual
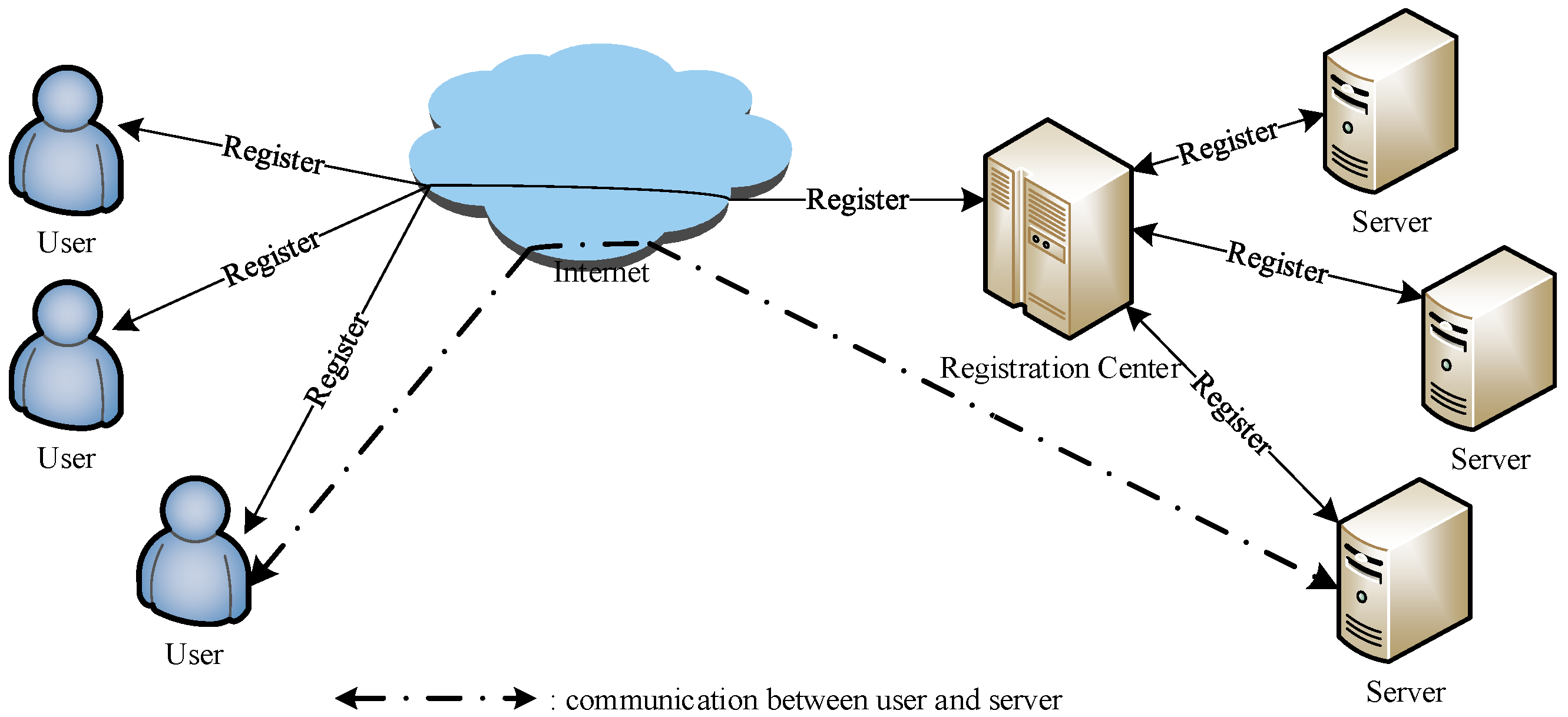
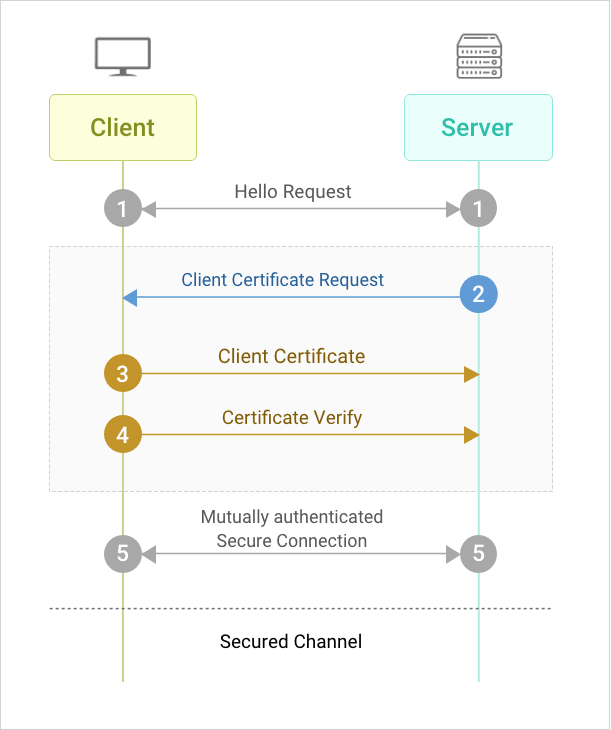
Sensors | Free Full-Text | A Multi-Server Two-Factor Authentication Scheme with Un-Traceability Using Elliptic Curve Cryptography
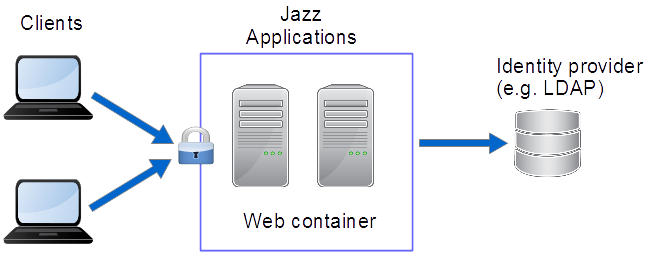
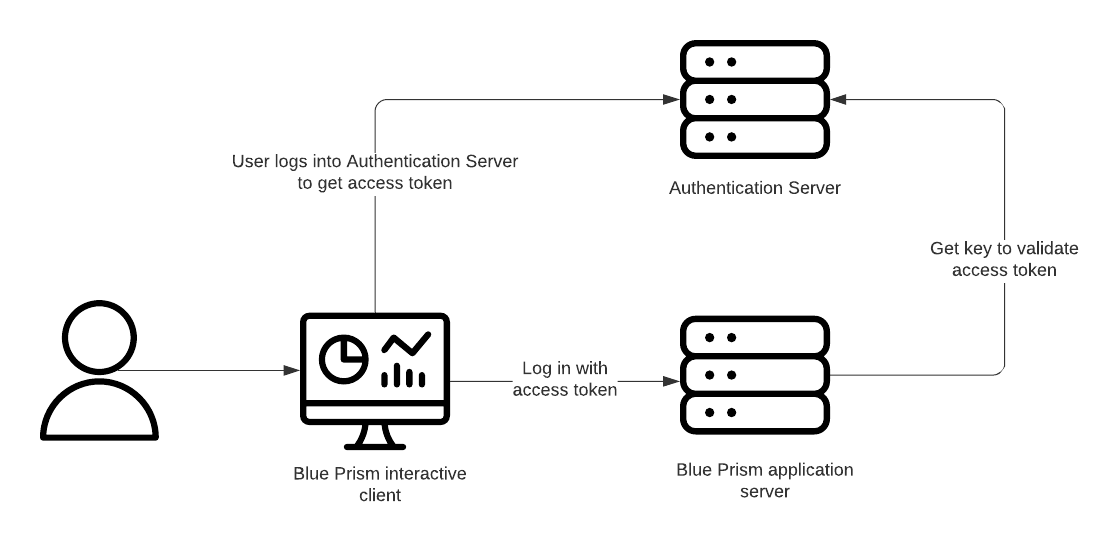
Bizagi Studio > Security definition > Work Portal Security > Work Portal Authentication > OAuth authentication
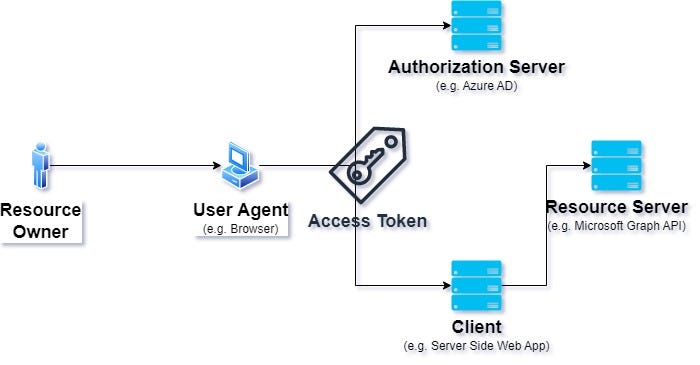
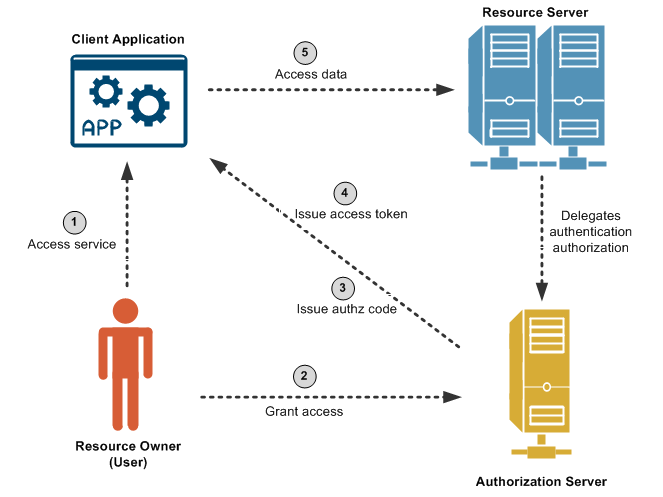
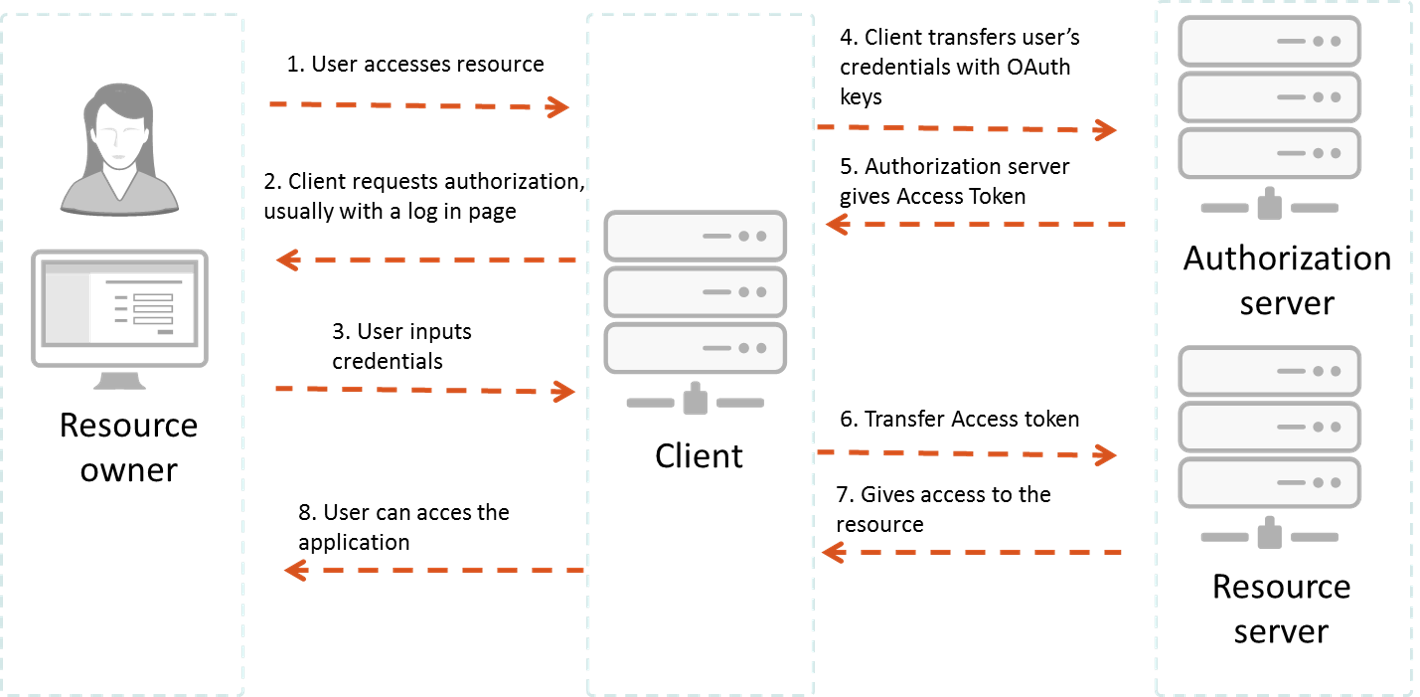
Understanding OAuth 2.0: Architecture, Use Cases, Benefits, and Limitations (Part 1) | by Anirban Bhattacherji | ITNEXT
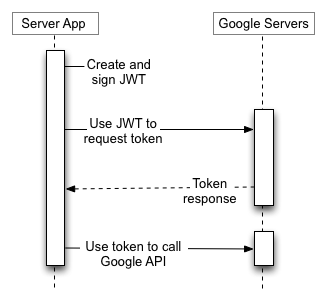
Understanding OAuth2 and Building a Basic Authorization Server of Your Own: A Beginner's Guide | by Ratros Y. | Google Cloud - Community | Medium
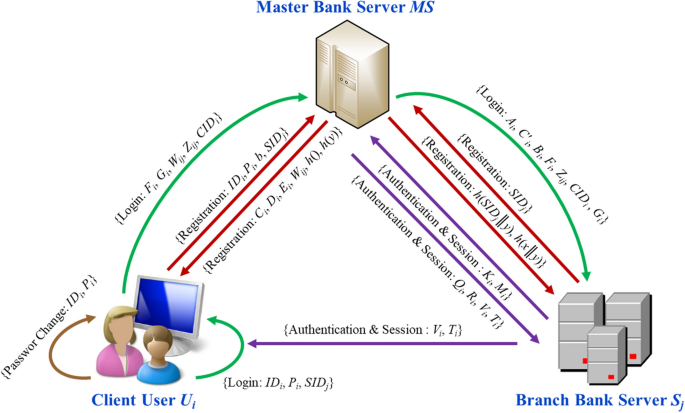
The application of multi-server authentication scheme in internet banking transaction environments | SpringerLink